When you use the word ‘legacy’ it can conjure up all sorts of images – from something important and positive being passed down generations (such as a business or tradition) to a more negative idea of bad practice continuing through habitual use. Overall, the word ‘legacy’ is neutral – it depends on the circumstances and subject involved for a good or bad outcome.
Much the same is true in the security sector. We often refer to ‘Legacy Systems’ and simply mean components that have been passed on from previous security operators or networks or components in the system that is based on older or non-current technology – whether they are good or bad is highly subjective. However, these legacy elements do require careful consideration when it comes to ensuring security systems are totally fit for purpose.
Inherited Equipment
The electronic security industry is not a new one anymore – access control companies like TDSi have been around since the early 1980s (we started in 1982 and many others were established during the 1980s and 1990s as technology advanced rapidly).
In more recent years the security industry has gone from an analogue world to a digital one, which has brought many advantages in terms of usability and reliability. The analogue world did have some advantages though, for example, it was full of closed protocols and was very easy to secure and difficult to crack.
Integrated systems and the advent of IP solutions over a decade ago, have allowed more and more integration, which is, of course, a good thing. It allows us to generate more data and use data mining to look at the relationship between data sets – which hitherto we were unable to realistically analyse in granular detail before.
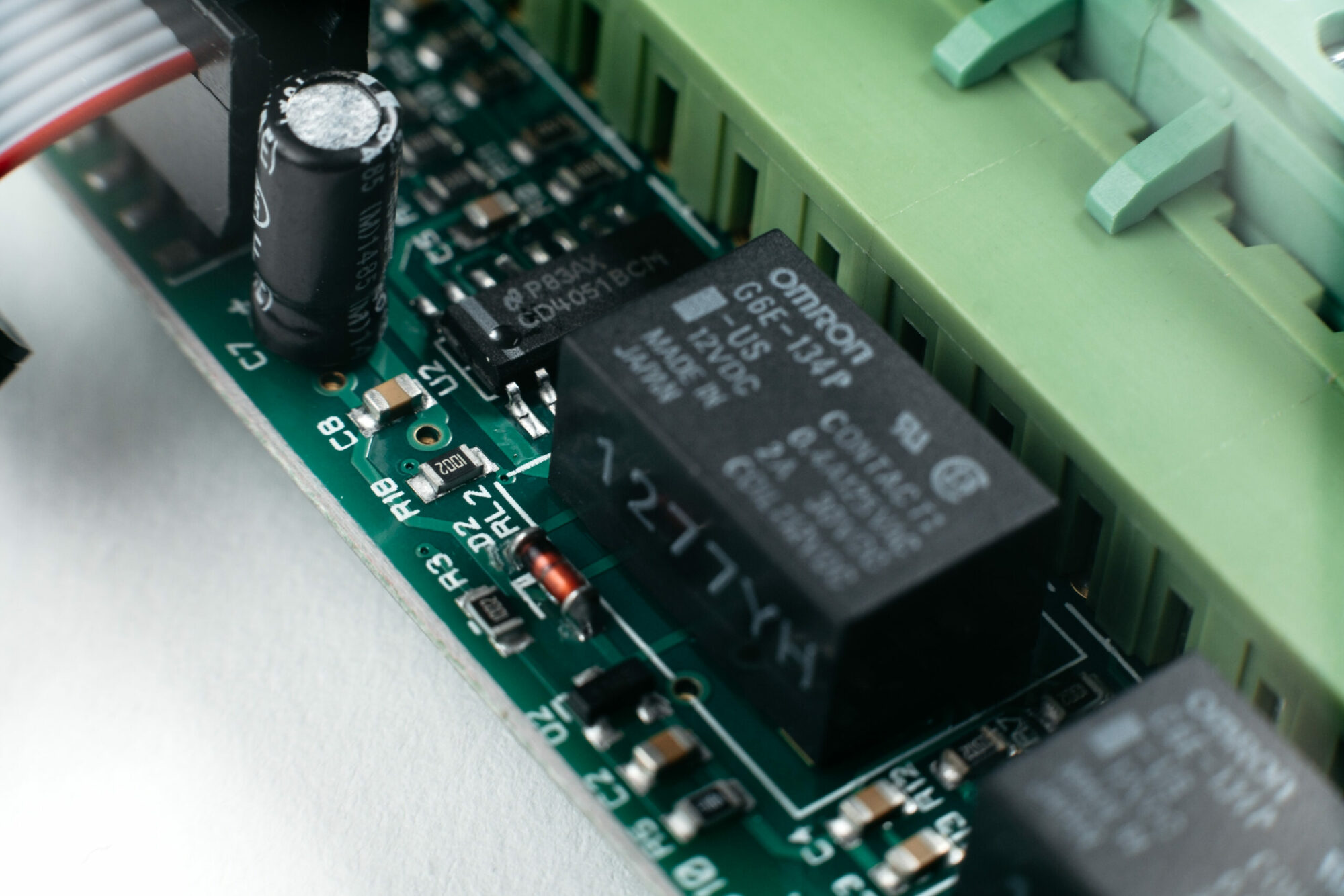
This integration includes many pre-integration systems and there are a lot of legacy systems out there that are now being brought into the IP world. For example, this is often the case with specialised detection systems or those in places that are difficult to access for upgrades (such as a nuclear plant or dangerous chemicals facility for example).
Ensuring Parity
When systems or installations are being upgraded and improved, it’s very important for IP security to be considered in detail. This means understanding any inherent vulnerabilities from all the components, but especially the legacy systems. This is further complicated when they are installed at several sites and networked through a centralised security system.
Often this knowledge is not in the domain of the end-user, despite using these older systems for some time. However, it should be within the domain of the security installers and maintainers. Unfortunately, with technology development moving so quickly, some installers may simply not be 100% up to speed with the latest threats or their potential impact on older technology.
Expert Overview
When it comes to including and (just as vitally) securing legacy systems within a modern mix of technology, it is vital there is a proper understanding of the wider picture. There is a big role here for consultants to play in evaluating legacy systems, providing advice to end-users and maintainers on what needs to be done to bring these elements into a modern, cyber-secure world.
There are many ways to ensure the security of legacy systems, it could be adding specific firewall-type barriers between them and core security data systems, and it may involve storing their data at the edge of the network and securely collecting it separately. This can compromise some of the integration benefits and cause potential issues, but the security of the whole network needs to take precedence over the benefits of individual legacy components.
Combining Old & New
The inclusion of legacy systems can bring considerable benefits for security operators. They give flexibility to the installation design and they often bring benefits in the case of specialist components. Inevitably there is also often a considerable cost benefit involved with re-using older equipment and environmental advantages to recycling components.
The main issue is that many of these systems were produced without the knowledge of modern highly connected networks and simply don’t have the inbuilt protection we have come to expect today.
This certainly doesn’t mean legacy equipment must automatically be consigned to the scrapheap, but it does mean careful consideration is needed to ensure it provides a true positive legacy rather than a potentially dangerous one.
Other News
News 23/04/2024
Making the Most of a Show
The Security Event 2024 is taking place from 30th April to 2nd May, so all eyes will be on the NEC Birmingham as a showcase…
Read moreNews 23/04/2024
TDSi Introduces Software Migration Programme for EXgarde Platform to Latest GARDiS Software
TDSi announces the introduction of a new software migration programme from its venerable EXgarde platform to the latest version of its powerful and flexible GARDiS…
Read moreNews 23/04/2024
EXgarde Software End of Life Statement
When our EXgarde Platform was introduced back in 2001, it was at the cutting edge of Access Control Software and offered many innovative features and…
Read more